Why Google's Latest Move Might Inspire You to Replace Chrome
A troubling report reveals that Google has quietly installed a 4GB AI model on users' computers—yours included.
Cybersecurity threats, protection strategies, and best practices
A troubling report reveals that Google has quietly installed a 4GB AI model on users' computers—yours included.

Explore these intriguing series set in captivating small towns, blending mystery with engaging storytelling.
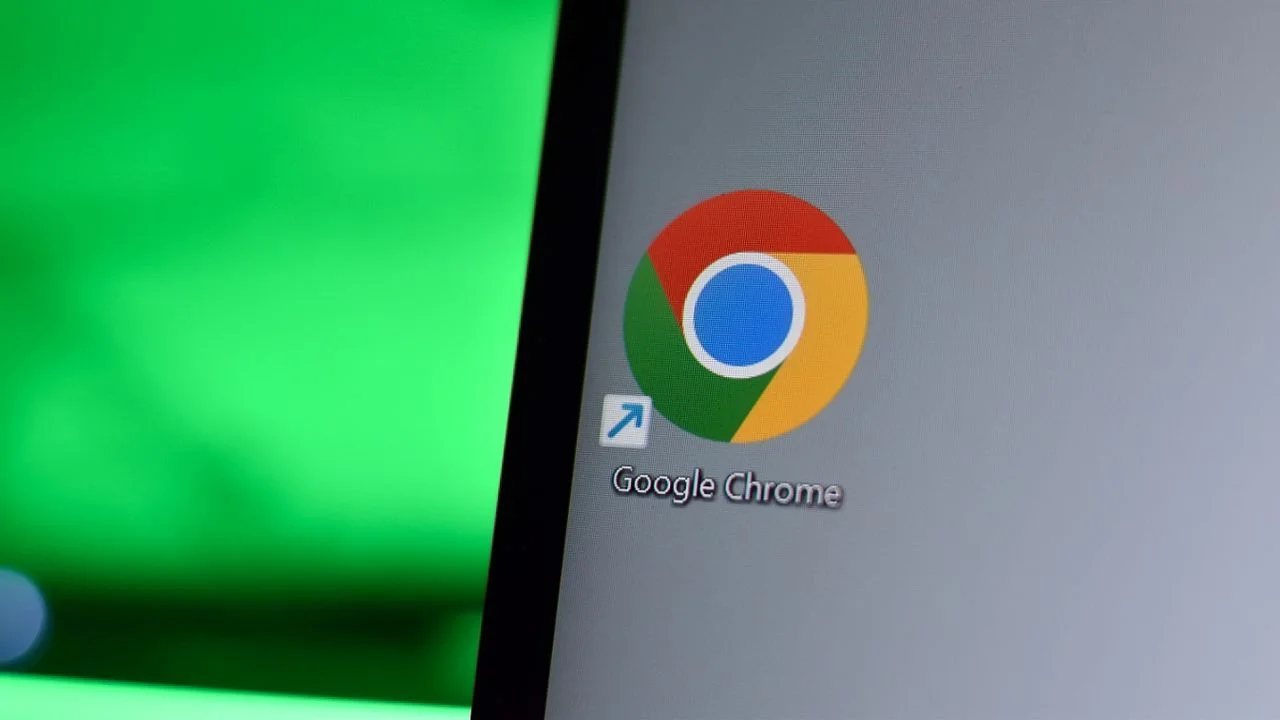
Google addresses the evolving landscape of cyber threats by leveraging agentic threat intelligence to enhance defense strategies. Our vision emphasizes proactive measures that elevate cybersecurity standards.

Researchers at Trend Micro have revealed a novel malware framework that enables attackers to convert Linux systems into hidden supply chain distribution networks, designed to withstand takedown efforts.

With the rapid adoption of internal LLMs, AI assistants, and autonomous systems, discussions around security increasingly highlight emerging threats, including prompt injection and data vulnerabilities, requiring urgent attention from organizations.

St. Michael’s Hospital in Toronto conducted a full-scale Code Orange simulation, involving all clinical and operational teams to test their readiness for mass casualty scenarios, highlighting the importance of preparedness in high-stakes environments.

Dynamic and Static Application Security Testing tools empower developers to enhance their source code security. Discover our selection of the best solutions available for this purpose.
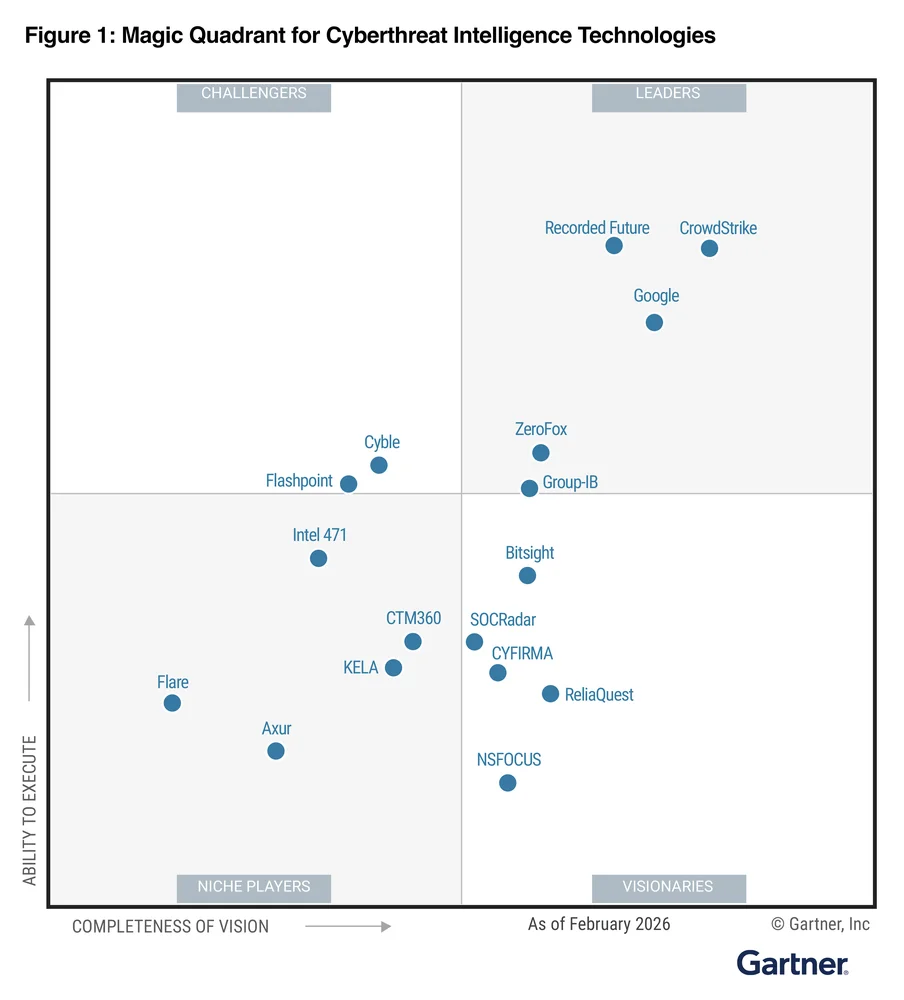
Developing AI agents for demonstrations is straightforward, but deploying them in real-world settings demands robust infrastructure. At Google Cloud Next '26, we showcased the Gemini Enterprise Agent Platform, highlighting tools and resources to facilitate efficient production environments for AI agents.
Google Cloud Next introduced Agent Gateway to simplify the management of agents, tackling the complexities and security risks associated with AI actions. This ecosystem streamlines oversight while fortifying governance measures.

Effective design prioritizes functionality as it influences aesthetics. When users must engage with system tools, their usability directly impacts user satisfaction and overall experience.

If you're relying on Samsung Messages, ensure you back up your conversations before the July deadline.
The healthcare sector is transforming as electronic health records (EHRs) and essential applications transition to web-based platforms, positioning the browser as a vital tool for patient care.
The Rust Project continues to enhance its commitment to open-source development by participating in Outreachy, complementing its three-year involvement in initiatives like Google Summer of Code.
Discover practical techniques to enhance your internet browsing with Opera, boosting your efficiency and enjoyment online.
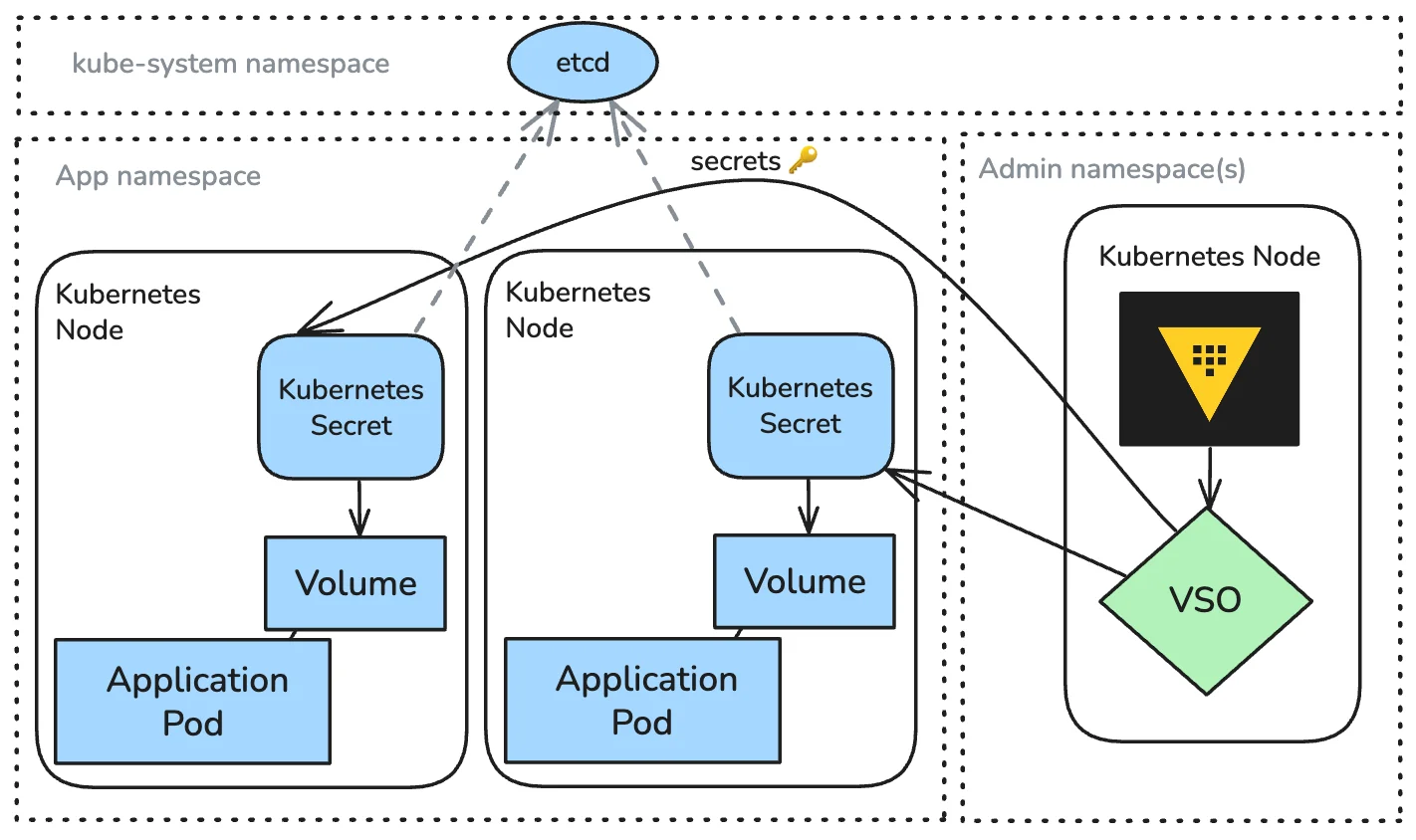
Discover how HashiCorp Vault Secrets Operator (VSO) streamlines secret delivery in Kubernetes and Red Hat OpenShift, facilitating secure automated lifecycle management on a large scale.

As Google I/O approaches, we outline expected advancements and features that could redefine user experiences.
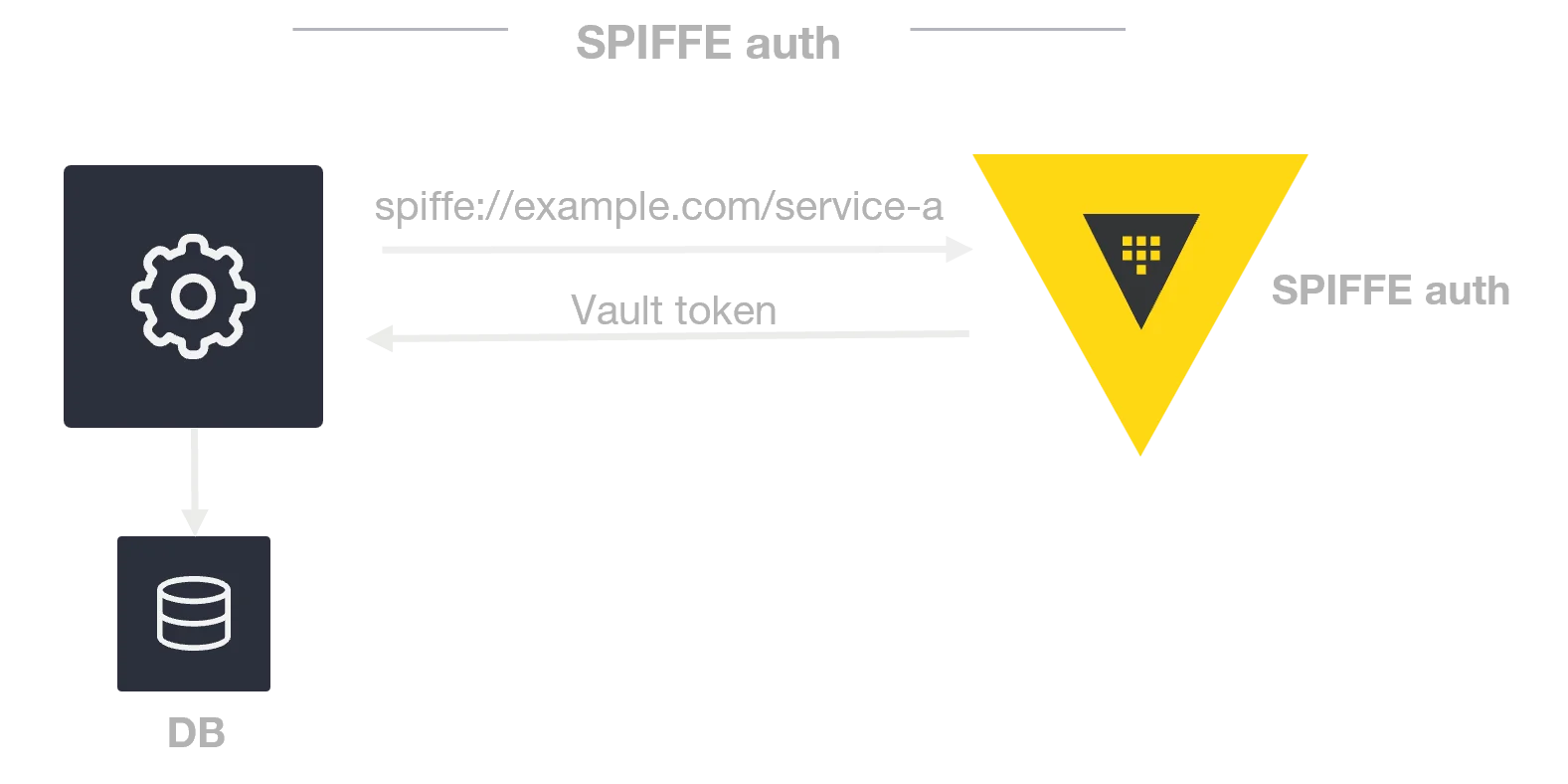
Vault Enterprise leverages native SPIFFE authentication to streamline and enhance the security of non-human identity (NHI) workloads, including AI agents.

HashiCorp introduces the Partner Premier status within the Terraform Registry, enhancing collaboration and streamlining access for top partners.
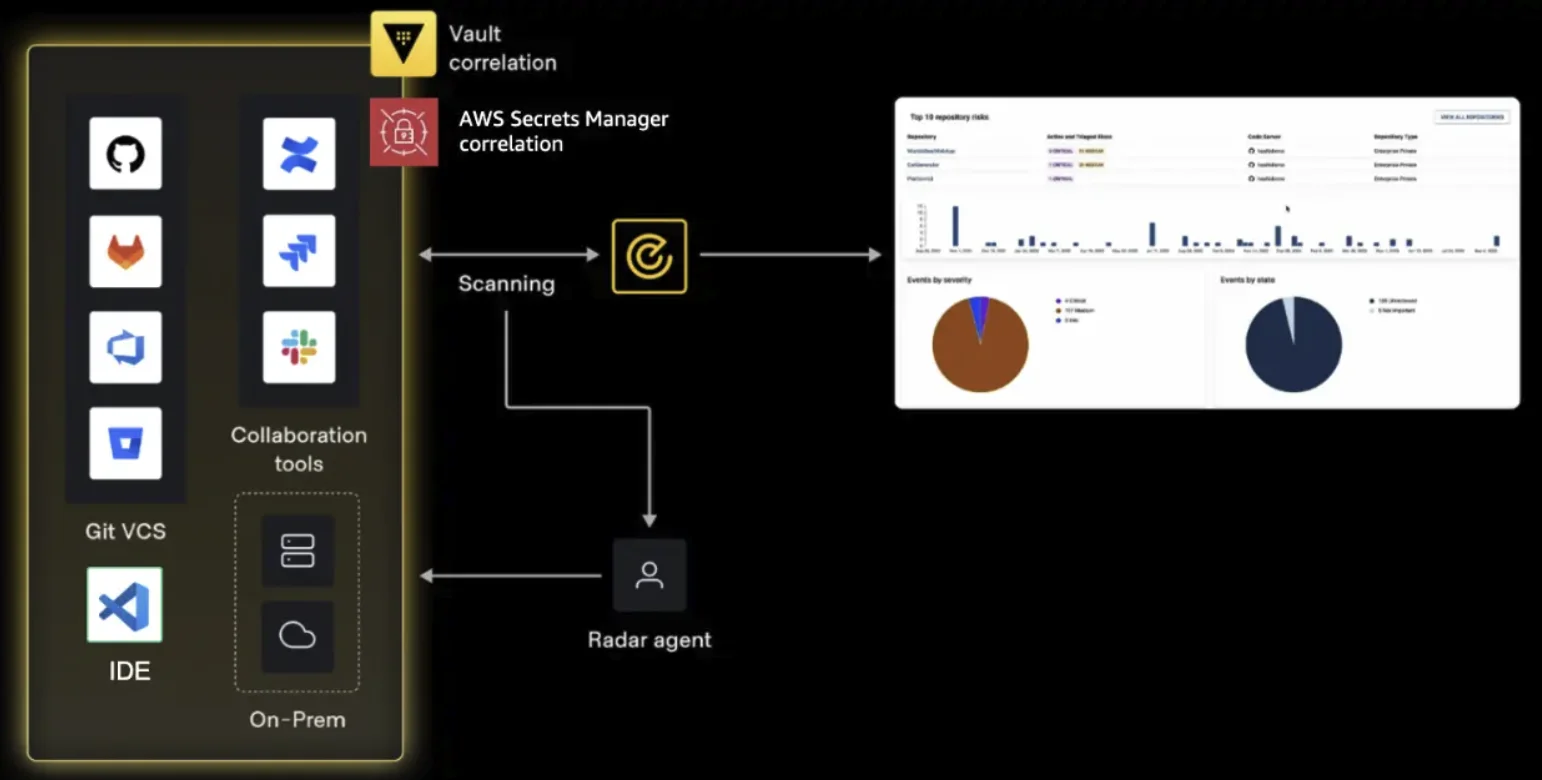
Secret detection uncovers credential sprawl, while targeted remediation minimizes associated risks. Vault Radar empowers teams to transition from identifying issues to implementing coordinated solutions.
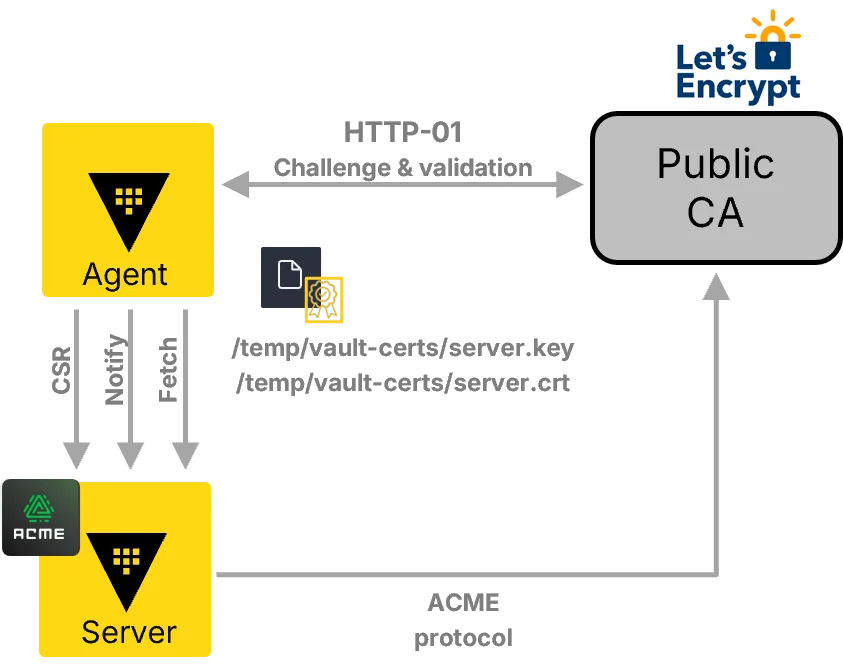
Discover how IBM Vault's public certificate integration automates public CA workflows, streamlines PKI lifecycle management, and secures internal processes efficiently.