In the increasingly complex landscape of cloud security, identifying secrets—credentials, API keys, and other sensitive information—within your code repositories and deployment environments is only half the battle. Organizations today grapple with how to effectively manage those secrets once they are discovered. The real challenge lies in connecting detection to a well-defined remediation process that spans multiple teams and systems. The shortcomings of current methodologies in addressing this problem reveal gaps in accountability, workflow alignment, and measurable improvement that, if left unaddressed, can lead to significant security risks.
Navigating the Secrets Dilemma
When a secret is flagged, teams must quickly ascertain its relevance: Is it already controlled and secure, or does it pose a potential risk because it isn't managed properly? Traditional secret detection processes overlook this nuance, leaving organizations with an unclear remediation path. Enter HashiCorp’s Vault Radar, which aims to bring clarity and structure to this chaotic workflow.
Vault Radar distinguishes between actively managed secrets and those that are outside established protocols. By correlating findings with centralized secret management systems like Vault and AWS Secrets Manager, organizations can understand whether a secret, once exposed, requires immediate remediation or whether it falls under existing governance frameworks. This correlation is crucial: it allows teams to prioritize which secrets need urgent attention based on their context, thus streamlining the remediation process.
Webhooks: Integrating with Established Workflows
Communication between teams is another significant challenge. Most organizations do not manage remediation within a single platform, leading to fragmented responsibilities and slow response times. Vault Radar addresses this operational gap with webhook support, enabling real-time event notifications that can directly integrate into existing workflows. This capability means that findings from secret detections can automatically trigger ticketing systems, alerts in collaboration tools, or even initiate other automated responses.
The efficiency gained through such integrations cannot be overstated. When teams can respond to discovered secrets using the tools they already rely on, the friction between detection and remediation diminishes significantly. This seamless integration ensures that secret remediation becomes a part of the operational fabric of the organization rather than an isolated task.
Remediation Reporting: Monitoring Progress Effectively
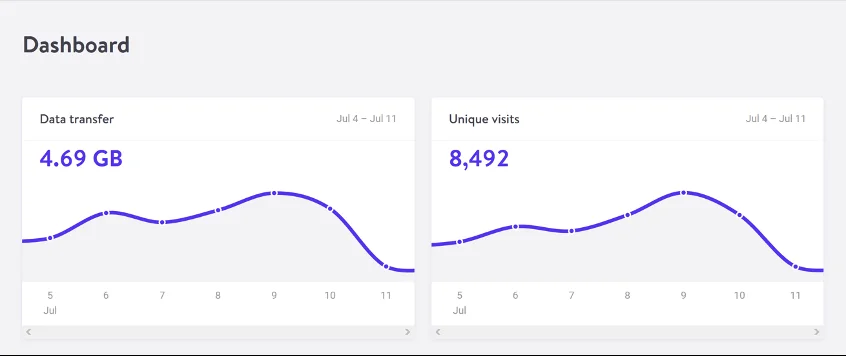
As organizations ramp up their secret detection capabilities, understanding the effectiveness of remediation efforts becomes crucial. Remediation reporting allows teams to visualize their progress by showcasing statistics such as newly discovered secrets, resolution timelines, and the overall efficiency of their processes. By shifting the focus from merely counting exposed secrets to demonstrating how effectively risk is being mitigated, security leaders can gain valuable insights into the health of their secret management practices.
This report-driven approach enables organizations to identify bottlenecks, assess how swiftly they are resolving issues, and adjust their strategies accordingly. It reflects not only on individual performance but also on the organization's capacity for proactive risk management.
Traceability: Creating a Clear Path for Accountability
For effective remediation, traceability is vital. By keeping a historical record of each secret from the moment it is detected until it is resolved, organizations can ensure accountability across the board. This visibility helps establish a unified understanding of the actions taken, the timeframes involved, and the performance of different teams in handling security issues.
Such traceability is not merely a convenience; it becomes a critical element for both forensic analysis and compliance. Having a detailed record allows teams to conduct thorough post-incident reviews, demonstrating that remediation protocols were followed and making the organization better prepared for audits or external scrutiny.
Toward Measurable Security Outcomes
Detection is merely the starting point in the lifecycle of secret management, but as organizations have repeatedly discovered, the outcomes hinge on how effectively they act on their findings. Vault Radar provides a framework that connects detection with actionable remediation, enhancing coordination across teams, clarifying roles and responsibilities, and ensuring measurable progress against security risks.
The real value of a tool like Vault Radar becomes evident when it transcends mere detection and empowers organizations to structure their workflows in a way that consistently strengthens their security posture. This proactive approach not only minimizes exposure but also builds a foundation for long-term resilience against security threats. The stakes have never been higher, and organizations are best served when their processes are as sophisticated as the threats they seek to defend against. By adopting more robust secret management strategies today, companies can effectively reduce risks and set themselves up for success in an expansive digital landscape.
For those involved in developing security policies or technology implementations, the features offered by Vault Radar serve as a significant advancement in how organizations can approach secret management. Engaging with these technologies may very well be the difference between a reactive stance on security and a proactive one, where risks are mitigated before they escalate into full-blown incidents.