In heavily regulated sectors like finance, healthcare, and critical infrastructure, ensuring meticulous scrutiny of privileged access isn't just best practice—it's a requirement. Compliance with regulations such as SOX, DORA, PCI DSS, and HIPAA mandates comprehensive activity logging and the capacity to promptly detect suspicious actions. As organizations enhance their security frameworks, the need for richer insights into privileged access behaviors becomes imperative.
HashiCorp's Boundary has made inroads by offering identity-based access control, session brokering, and detailed session recordings. However, security teams are increasingly recognizing that video footage alone isn't sufficient for rapid incident response. They require actionable, real-time data in structured formats that can be easily ingested by Security Information and Event Management (SIEM) platforms, facilitating immediate detection and incident prioritization.
Understanding the Limitations of Session Recordings
Boundary’s session recordings deserve their nod of approval for the exhaustive detail they provide during forensic examinations. Security analysts can scrutinize user activities, down to the keystrokes and commands executed. Yet, here's the thing: SOCs don't kick off their investigations by watching these recordings; they need alerts driven by structured data. Without proper contextualization, critical evidence captured in these recordings risks going unnoticed until it's too late.
Imagine a situation where a privileged user interacts with a production database and initiates high-risk commands, such as accessing sensitive files or attempting privilege escalation. If festive auditors miss capturing those actions as alerts in their SIEM systems, they will never leverage the insights that live within Boundary's recordings. Hence, organizations are faced with a dual-faceted challenge: generate real-time alerts for high-risk activities and utilize session recordings for in-depth investigations post-event.
Proposed Solution: Integrating Kernel-Level Auditing
To tackle this obstacle efficiently, organizations can deploy Elastic's Auditbeat alongside Boundary. Rather than attempting the cumbersome task of converting video recordings into structured text—a process fraught with inaccuracies—Auditbeat captures audit events directly from the kernel, contextualized and ready for immediate security monitoring.
Key Capabilities of Auditbeat
When integrated with Linux-based hosts, Auditbeat provides a treasure trove of actionable data:
- Process Execution: It logs every command executed including context-rich details like user identities and command results.
- File Access Monitoring: Unauthorized reads or writes to sensitive files, such as configuration files and passwords, can be tracked consistently.
- Privilege Escalation Attempts: Every invocation of
sudoorsu, whether successful or not, is meticulously documented. - User and Session Context: Captures the metadata necessary to understand which user engaged in activities and the environment in which they operated.
This structured information is emitted in JSON format, which is seamlessly compatible with any SIEM that supports JSON ingestion, including popular options like Elasticsearch and Splunk. The tactical implementation of Auditbeat provides organizations with a direct path to robust event monitoring while facilitating compliance auditing.
Why This Across-the-Board Approach is Effective
What sets this strategy apart is its practicality. Auditbeat is not only a production-proven tool but also operates with minimal overhead on contemporary systems. Its widespread adoption across enterprise infrastructures allows for SIEM-agnostic application, empowering organizations without confining them to proprietary systems. The architecture aligns with existing security strategies many enterprises already have in place, enabling quick deployment and immediate utility.
While HashiCorp is also working on integrating its own audit event collection with Boundary, leveraging Auditbeat offers an immediate, reliable solution for enterprises—addressing both compliance needs and operational efficiency concerns in real-time monitoring of privileged access. The result is a coherent system that produces tangible results for security analysts.
Correlation and Monitoring: Bridging the Gap
When an alert surfaces within the SIEM sourced from Auditbeat's data, crucial contextual details accompany it, simplifying the task of correlating it with specific Boundary session recordings. The insights drawn from this dual-system integration substantially streamline incident responses:
- Timestamp: Marks when the event occurred.
- Target Host: Identifies the system accessed during the session.
- OS User: Displays the user behind the activity.
- Commands or Files Accessed: Highlights what actions triggered the alert.
Security analysts can then efficiently pinpoint the corresponding Boundary session recording, providing them with a complete picture of the privileged actions taken before, during, and post-alert.
Enhancing Correlation with Embedded Metadata
For organizations utilizing Boundary Enterprise in conjunction with Vault—particularly for SSH certificate management—identity and context information can be directly embedded into logs. This ease of integration significantly advances the practicality of establishing relationships between SIEM alerts and the corresponding session data. With identifiable key IDs that incorporate project and user details, analysts can rapidly establish the origin of actions and correlate observations effectively.
Implementing the Architecture: A Hands-On Approach
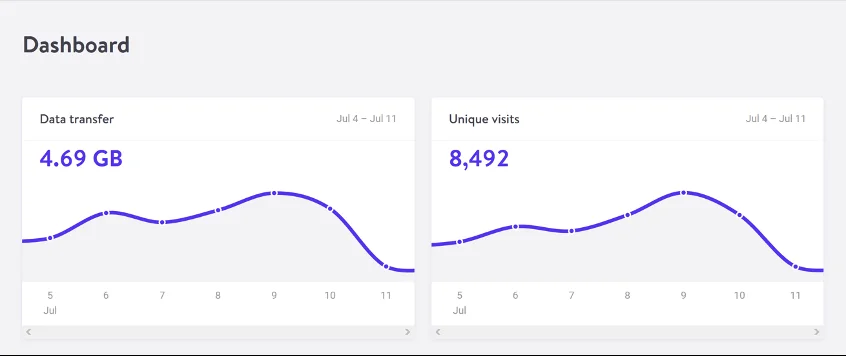
For organizations eager to adopt this architecture, a comprehensive demo environment is available via Docker. This reference implementation includes automated configurations for Boundary, Auditbeat, and Kibana, among other components. Users can immediately visualize the correlation between system alerts and session recordings, fostering a deeper understanding of how privileged access monitoring can be more robust.
Moving Past Limitations
While this architecture is designed for immediate deployment, it's critical to acknowledge certain constraints. The process of correlating alerts with recordings isn’t fully automated yet. Analysts still require context specifics—timestamp, user, and target metadata—to draw connections. Another challenge lies in managing accounts shared by multiple users, where the architecture offers contextual identifiers but can still lead to ambiguity. Additionally, a direct correlation using session ID remains in development, necessitating continued enhancement of these integrations.
Looking Ahead: The Future of Privileged Access Monitoring
The upcoming enhancements aimed at integrating Boundary with more refined audit capabilities show promising horizons for privileged access monitoring. As HashiCorp continues to innovate, we can expect not only greater fluidity in alert and session correlations but also a potential move towards optimized workflows that require reduced manual intervention. In this evolving landscape, staying ahead means adopting proven strategies while being receptive to forthcoming advancements.